What are the NIST SP 800-171 DoD Assessment Requirements?
For any organization doing business with the Department of Defense (DoD) and handling Controlled Unclassified Information (CUI), understanding the NIST SP 800-171 DoD Assessment Requirements isn’t optional – it’s a contractual mandate. With professional CMMC compliance Florida, These requirements outline the formal process by which the DoD evaluates a contractor’s implementation of the 110 security controls detailed in NIST Special Publication 800-171. Beyond simply having controls in place, the DoD wants assurance that these measures are effectively protecting sensitive unclassified data. These assessments are critical because they directly impact your eligibility for current and future defense contracts, serving as a transparent mechanism for the DoD to gauge the cybersecurity posture of its vast supply chain. It’s about building trust and ensuring the integrity of critical national security information.CMMC DoD Contractors wanting to learn what level of CMMC depends on FCI and CUI. Download our CMMC Ebook to help navigate the CMMC requirements and expectations. We are here to help you obtain certification when needeed.
hbspt.forms.create({ portalId: “47377746”, formId: “720a0b73-e9ab-459f-893a-ca2e89407469” });Since 2017 the DoD has been stuck between a rock and a hard place. With the vast number of DoD contractors, diverse IT infrastructure, and continuously evolving IT environment the DoD how do you ensure that you are truly secure? Unfortunately, the DoD has been forced to rely on contractors to self-attest, perform POA&Ms, and haven’t had anywhere near enough bandwidth to audit each contractor to make sure they are truly compliant with all 110 requirements of the framework. That changes this year with the implementation of the DoD’s new CMMC requirement.
Basic CMMC Compliance begins with 110
Starting November 30, 2020, all contractors and their subs will need to have a score representing their NIST 800-171 progress ranked from level 1 through level 5 published in a federal database before contract award. Plus, the score needs to be accompanied by the date in which all requirements are being implemented and screenshots showing compliance. This is the first step in a long road to securing our nation’s cyber infrastructure.
Right now, the DoD is using a vendor report card maintained in the Supplier Performance Risk System (SPRS) to determine compliance. This system will provide the DoD a snapshot of the contractor’s IT environment and allow them to “verify that an offeror has a current (i.e., not more than three years old, unless a lesser time is specified in the solicitation) Assessment, at any level, on record prior to contract award.”.
This “assessment” refers to the score generated by performing a review of your NIST 800-171 implementation as documented in your System Security Plan. “The NIST SP 800-171 DoD Assessment Methodology provides for the assessment of a contractor’s implementation of NIST SP 800-171 security requirements, as required by DFARS clause 252.204-7012.”
One important note before you can begin your CMMC compliance, you absolutely need to have a System Security Plan in place before you perform this assessment. It’s a mandatory requirement in the NIST 800-171, the regulation behind the compliance. In fact, without one, you are immediately deemed non-compliant! “The absence of a system security plan would result in a finding that an assessment could not be completed due to incomplete information and noncompliance with DFARS clause 252.204-7012.” – NIST SP 800-171 Assessment Methodology Version 1.2.1 Annex A Comment 3.12.4
You don’t want to get caught lying about this. As a representative of the Government you now have the whole False Claims Act thing to deal with. Luckily, if you still need an SSP, GiaSpace can help!
The Levels of CMMC Compliance
There are multiple levels of compliance. For now, the Government is mostly requiring CMMC level 1 for all of their contractors in the Process and Practice realms. However, different or future contracts may require different levels of CMMC compliance. It’s important to remember that in order to reach a specific level of compliance, you need to meet the level for both Process and Practice.
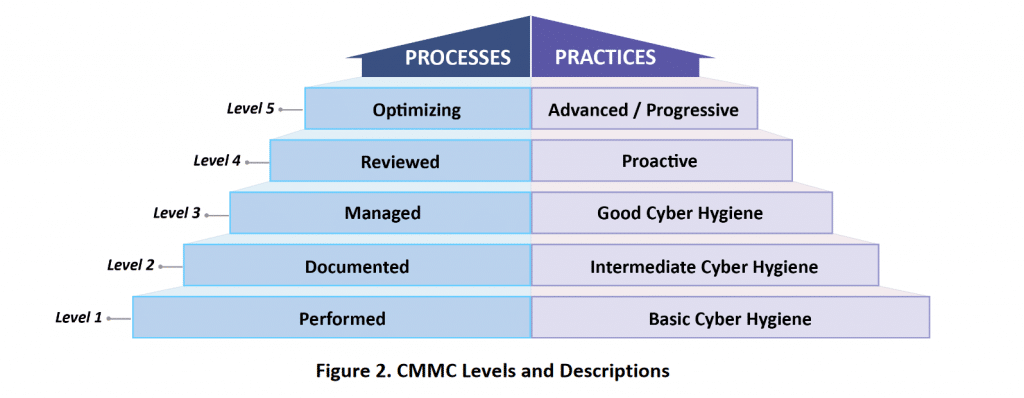
CMMC Level 1
Processes: Performed
Level 1 requires that an organization performs the specified practices. Because the organization may be able to perform these practices only in an ad-hoc manner and may or may not rely on documentation, process maturity is not assessed for Level 1.
Practices: Basic Cyber Hygiene
Level 1 focuses on the protection of FCI and consists only of practices that correspond to the basic safeguarding requirements specified in 48 CFR 52.204-21.
CMMC Level 2
Processes: Documented
Level 2 requires that an organization establish and document practices and policies to guide the implementation of their CMMC efforts. The documentation of practices enables individuals to perform them in a repeatable manner. Organizations develop mature capabilities by documenting their processes and practicing them as documented.
Practices: Intermediate Cyber Hygiene
Level 2 serves as a progression from Level 1 to Level 3 and consists of a subset of the security requirements specified in NIST SP 800-171 as well as practices from other standards and references. Because this level is a transitional stage, a subset of the practices reference the protection of CUI.
CMMC Level 3
Processes: Managed
Level 3 requires that an organization establish, maintain and resource a plan demonstrating the management of activities for practice implementation. The plan may include information on missions, goals, project plans, resourcing, required training, and involvement of relevant stakeholders.
Practices: Good Cyber Hygiene
Level 3 focuses on the protection of CUI and encompasses all of the security requirements specified in NIST SP 800-171 as well as additional practices to mitigate threats. Note that DFARS clause 252.204-7012 applies, and specifies additional requirements beyond NIST SP 800-171 security requirements such as incident reporting.
CMMC Level 4
Processes: Reviewed
Level 4 requires that an organization review and measure practices for effectiveness. In addition, organizations at this level are able to take corrective action when necessary and inform higher level management of status or issues on a recurring basis.
Practices: Proactive
Level 4 focuses on the protection of CUI from APTs and encompasses a subset of the enhanced security requirements from Draft NIST SP 800-171B as well as other cybersecurity best practices. These practices enhance the detection and response capabilities of an organization to address and adapt to the changing tactics, techniques and procedures (TTPs) used by APTs.
CMMC Level 5
Processes: Optimizing
Level 5 requires an organization to standardize and optimize process implementation across the entire organization.
Practices: Advanced/Proactive
Level 5 focuses on the protection of CUI from APTs. The additional practices increase the depth and sophistication of cybersecurity capabilities.
It’s important to remember that each level is cumulative. For example, in order to reach CMMC level 3 you must show that you have successfully reached CMMC levels 1 and 2 and it must be reached on both the Practice and Process realms.
You also need to remember that this needs to flow down through all of your subcontractors! Now this doesn’t mean that if you have a CMMC level 5 certification that all of your subcontractors will need to have the same level certification, but it does mean that each of your subcontractors will be required to at least maintain a level 1 certification.
Why are DoD Assessments for NIST 800-171 Mandatory?
The shift from self-attestation to mandatory DoD assessments for NIST 800-171 was driven by a clear and urgent need: to strengthen the cybersecurity of the entire Defense Industrial Base (DIB). The consequences of cyber breaches within the supply chain can be severe, impacting national security and costing millions. These assessments are now mandatory for several compelling reasons:
-
Protecting Controlled Unclassified Information (CUI): The primary driver is safeguarding sensitive CUI that resides within non-federal systems. This data, while not classified, is vital to DoD operations and can be exploited by adversaries if compromised.
-
Enforcing DFARS Clauses: Specific Defense Federal Acquisition Regulation Supplement (DFARS) clauses, particularly DFARS 252.204-7019 and 252.204-7020, explicitly mandate these assessments. Non-compliance means violating contractual terms.
-
Ensuring Supply Chain Integrity: A single vulnerable link in the defense supply chain can compromise the entire network. Assessments provide the DoD with assurance that contractors are actively protecting their systems.
-
Standardized Verification: They move beyond self-attestation, providing a standardized, objective methodology for verifying a contractor’s cybersecurity maturity. This gives the DoD a clear picture of risk across the DIB.
-
Preparation for CMMC: While distinct, these assessments lay the foundational groundwork for the upcoming Cybersecurity Maturity Model Certification (CMMC) 2.0. Achieving a strong assessment score is a direct step towards CMMC Level 2 certification.
In essence, mandatory DoD assessments ensure that defense contractors are not just aware of cybersecurity best practices, but are actively implementing and proving their adherence to protect the nation’s critical information.
What are the three levels of NIST 800-171 DoD Assessments? (Basic, Medium, High)
The DoD utilizes a tiered approach to assessing NIST 800-171 compliance, providing varying levels of confidence in a contractor’s cybersecurity posture. Understanding these three assessment levels — Basic, Medium, and High — is crucial for defense contractors.
-
Basic Assessment (Self-Assessment):
-
Description: This is a self-assessment conducted by the contractor. It involves reviewing your System Security Plan (SSP) and your Plan of Action & Milestones (POA&M) against the 110 NIST SP 800-171 controls.
-
Confidence Level: Low confidence. While mandatory, the DoD relies on the contractor’s honest and accurate representation of their security posture.
-
Frequency: At least every three years (as mandated by DFARS 252.204-7019/7020), or whenever significant changes occur in your CUI environment.
-
Outcome: A numerical score (out of 110) is derived and reported to the Supplier Performance Risk System (SPRS).
-
-
Medium Assessment (DoD-Led Remote Assessment):
-
Description: Conducted by the Defense Contract Management Agency (DCMA) Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) or other authorized DoD entities. This is primarily a remote assessment, involving a deeper dive into your SSP and POA&M, interviews with your personnel, and examination of supporting documentation (e.g., policy documents, configuration settings, audit logs).
-
Confidence Level: Medium confidence. This provides a more objective validation of your self-assessment.
-
Trigger: Can be initiated by the DoD based on factors like contract value, criticality of CUI, or random selection.
-
Outcome: A formal assessment report and an updated score uploaded to SPRS.
-
-
High Assessment (DoD-Led On-Site Assessment):
-
Description: The most rigorous assessment, involving an on-site evaluation by the DIBCAC or other DoD teams. This includes in-depth interviews, comprehensive documentation review, physical inspection of facilities, and technical verification of implemented controls. Assessors will verify claims and often require live demonstrations of controls.
-
Confidence Level: High confidence. Provides the greatest assurance of compliance.
-
Trigger: Typically reserved for high-risk contracts, critical programs, or when a medium assessment raises significant concerns.
-
Outcome: A comprehensive assessment report and a validated score uploaded to SPRS.
-
Regardless of the level, the goal is always the same: to ensure the robust protection of Controlled Unclassified Information throughout the DoD supply chain.
How is your NIST 800-171 Assessment Score Calculated?
Understanding the scoring methodology for your NIST 800-171 DoD Assessment is crucial, as it directly impacts your standing with the Department of Defense. Unlike a simple pass/fail, this system provides a nuanced reflection of your compliance posture.
The scoring begins with a perfect score of 110 points, representing full implementation of all 110 security requirements outlined in NIST SP 800-171. For each requirement not fully implemented, points are subtracted from this baseline. It’s important to note that a negative score is possible.
The DoD’s assessment methodology assigns weighted values to each control based on its impact to the information system and the CUI it handles. This means not all unimplemented controls subtract the same number of points:
-
5-point deductions: These are for critical “Basic Security Requirements” that form the foundation of your cybersecurity. If these aren’t met, many other “Derived Security Requirements” become ineffective.
-
3-point deductions: Applied to Derived Security Requirements that have a significant, but perhaps more confined, effect on the security of the network and data.
-
1-point deductions: For other Derived Security Requirements where non-implementation has a lesser, but still impactful, effect.
Example: If you meet 108 of the 110 controls, but two critical 5-point controls are not implemented, your score would be . However, if you miss twenty 1-point controls, your score would be .
Key Takeaways:
-
Weighted System: Focus on implementing the higher-weighted controls first, as they have the biggest impact on your score and overall security.
-
Negative Scores are Possible: Don’t be alarmed if your initial self-assessment yields a negative score. It simply reflects the work ahead.
-
POA&Ms are Key: A Plan of Action & Milestones (POA&M) is critical for documenting how and when you will address unimplemented controls. While a negative score won’t immediately disqualify you, a robust POA&M demonstrates commitment to remediation.
This transparent scoring allows the DoD to gain a quantifiable understanding of a contractor’s cybersecurity readiness and drive continuous improvement across the DIB.
What is the Supplier Performance Risk System (SPRS), and why is it crucial?
The Supplier Performance Risk System (SPRS) is a web-enabled enterprise application serving as the Department of Defense’s single, authoritative source for supplier performance information. While it encompasses various aspects of supplier performance, its role in cybersecurity compliance, particularly with NIST 800-171, has become absolutely crucial for DoD contractors.
Why SPRS is Crucial for DoD Contractors:
-
Central Repository for Assessment Scores: Under DFARS clauses 252.204-7019 and 252.204-7020, contractors are mandated to submit their NIST SP 800-171 assessment scores (from their Basic Self-Assessment) into SPRS. This makes your cybersecurity posture visible to DoD contracting officers.
-
Contract Eligibility and Award: Your SPRS score directly influences your eligibility for new DoD contracts and task orders. Contracting officers are required to check SPRS and ensure your company has a current assessment (less than three years old) on file before awarding contracts involving CUI.
-
Risk Assessment for DoD: SPRS provides the DoD with a real-time view of cybersecurity risks across its supply chain. A low or missing score can signal higher risk, potentially leading to increased scrutiny or even disqualification.
-
Flow-Down Requirements: Prime contractors are now responsible for ensuring their subcontractors also have current NIST 800-171 assessment scores in SPRS, creating a cascading effect throughout the DIB.
-
Precursor to CMMC: SPRS will continue to be relevant for CMMC 2.0. While CMMC Level 2 will require third-party assessments, the foundational self-assessment data in SPRS is a key starting point.
In essence, SPRS acts as the DoD’s cybersecurity scorecard for its contractors. A current, accurately reported NIST 800-171 assessment score in SPRS is no longer just good practice – it’s a non-negotiable gateway to maintaining and securing DoD business.
What steps should you take to prepare for a DoD NIST 800-171 Assessment?
Preparing for a DoD NIST 800-171 Assessment, regardless of whether it’s a Basic self-assessment or a more in-depth Medium/High assessment, requires a methodical and proactive approach. Your readiness is paramount to a successful outcome and continued contract eligibility.
Here are the essential steps to prepare:
-
Understand the Requirements Thoroughly:
-
Familiarize yourself with NIST SP 800-171 Revision 2 and the DoD NIST SP 800-171 Assessment Methodology. These are your foundational documents.
-
Identify all 110 security controls and their objectives.
-
-
Define Your CUI Environment:
-
Conduct a comprehensive data inventory to identify where CUI resides, how it flows through your systems, and who has access to it. This defines your “assessment scope.”
-
Document your CUI assets, processes, and boundaries.
-
-
Conduct a Gap Analysis (Self-Assessment):
-
Perform an honest, objective self-assessment against all 110 NIST 800-171 controls. This is typically done using the DoD Assessment Methodology.
-
Identify which controls are fully implemented, partially implemented, or not implemented at all.
-
-
Develop/Refine Your System Security Plan (SSP):
-
Your SSP is a detailed document explaining how your organization implements each of the 110 NIST 800-171 controls. It should be current, accurate, and comprehensive.
-
Describe your system architecture, policies, procedures, and how they meet the requirements.
-
-
Create a Robust Plan of Action & Milestones (POA&M):
-
For every control not fully implemented, develop a POA&M. This document outlines specific tasks, responsible parties, resources, and target completion dates for remediation.
-
A well-structured POA&M demonstrates your commitment to continuous improvement.
-
-
Gather Evidence and Documentation:
-
Collect artifacts that prove implementation (e.g., policy documents, configuration screenshots, audit logs, training records, vulnerability scan reports). Organize these for easy access.
-
For Medium or High assessments, be prepared to demonstrate controls live.
-
-
Conduct Internal Drills/Mock Assessments:
-
Practice answering questions and demonstrating controls. This helps identify weak spots in your documentation or understanding.
-
-
Train Your Personnel:
-
Ensure all employees, especially those involved in CUI handling or system management, understand their roles and responsibilities related to cybersecurity and NIST compliance.
-
-
Consider Expert Assistance:
-
Don’t go it alone if you lack in-house expertise. Cybersecurity compliance specialists like GiaSpace can guide you through the process, perform pre-assessments, and help remediate gaps.
-
Proactive and thorough preparation is the cornerstone of a successful DoD NIST 800-171 Assessment.
What are the typical hurdles during a DoD NIST 800-171 Assessment?
Even with diligent preparation, defense contractors often encounter common hurdles during a DoD NIST 800-171 Assessment. Anticipating these challenges allows you to mitigate them effectively and streamline the assessment process:
-
Incomplete or Inaccurate Documentation (SSP/POA&M): This is the most frequent stumbling block. Assessors heavily rely on your System Security Plan (SSP) and Plan of Action & Milestones (POA&M). If these documents are outdated, vague, or don’t accurately reflect your implementation, it immediately raises red flags.
-
Solution: Treat your SSP and POA&M as living documents. Review and update them regularly. Ensure they provide clear, verifiable descriptions of how each control is met.
-
-
Lack of Evidence: Simply stating you meet a control isn’t enough; you need tangible proof. Many organizations struggle to produce specific evidence (e.g., audit logs, policy enforcement screenshots, vulnerability scan reports) when requested.
-
Solution: Establish a systematic approach to collecting and organizing evidence. Automate log collection and reporting where possible.
-
-
Misinterpretation of Requirements: The NIST 800-171 controls can be complex, and misinterpreting a requirement can lead to incorrect implementation or a false sense of security.
-
Solution: Leverage NIST SP 800-171A (the assessment procedures guide) for clarification. Consider engaging a third-party expert for an independent review or pre-assessment.
-
-
Scoping Issues: Not accurately defining the boundaries of your CUI environment can lead to either over-scoping (unnecessary effort) or under-scoping (leaving critical CUI unprotected).
-
Solution: Conduct a thorough CUI data flow analysis. Clearly document system boundaries and interconnections.
-
-
Limited Access to Personnel/Systems During Assessment: Delays in providing assessors access to key personnel for interviews or to systems for verification can prolong the assessment and create frustration.
-
Solution: Designate a dedicated assessment liaison. Ensure key personnel are available and informed of their roles during the assessment.
-
-
Unaddressed POA&M Items: While a POA&M is acceptable, assessors will scrutinize the progress and timelines for open items. Significant delays or lack of action on critical controls are concerns.
-
Solution: Actively work to remediate POA&M items. Provide regular updates on progress.
-
-
Technical Control Gaps: Fundamentally, some organizations simply haven’t implemented all the necessary technical or administrative controls.
-
Solution: Use the assessment as an opportunity for honest self-reflection and prioritize remediation. Seek expert help for complex technical implementations.
-
Addressing these common hurdles proactively will significantly improve your chances of a smooth and successful DoD NIST 800-171 Assessment.
How does the NIST 800-171 Assessment relate to CMMC 2.0?
The relationship between the NIST 800-171 Assessment and the Cybersecurity Maturity Model Certification (CMMC) 2.0 is a point of crucial importance for defense contractors. It’s not a matter of one replacing the other, but rather one building upon the other.
-
NIST SP 800-171 is the Foundation:
-
NIST SP 800-171 defines the security requirements for protecting Controlled Unclassified Information (CUI) in non-federal systems. It details 110 controls across 14 families.
-
The DoD NIST 800-171 Assessment Methodology (which you use for your Basic Self-Assessment and which the DoD uses for Medium/High assessments) is how the DoD measures your adherence to these 110 controls.
-
-
CMMC 2.0 is the Verification Model:
-
CMMC 2.0 is the DoD’s framework for verifying that defense contractors have implemented appropriate cybersecurity controls to protect CUI. It introduces a tiered approach to certification.
-
CMMC Level 2 (Advanced) is directly mapped to the 110 security controls of NIST SP 800-171. This means if you are aiming for CMMC Level 2, you must implement all 110 NIST 800-171 controls.
-
Key Connections and Differences:
-
Direct Alignment: For CMMC Level 2, the technical requirements are identical to NIST SP 800-171. If you’re compliant with 800-171, you’ve met the practice requirements for CMMC Level 2.
-
Assessment Mechanism:
-
Under DFARS, the NIST 800-171 Basic Assessment is a self-assessment, reported to SPRS. Medium and High assessments are DoD-led.
-
For CMMC Level 2, most organizations handling CUI will require a third-party assessment by a CMMC Third-Party Assessment Organization (C3PAO). This adds an independent layer of verification.
-
-
Mandatory Certification: CMMC 2.0 will make certification (based on your CMMC Level) a contractual requirement for DoD solicitations that involve CUI. Without the proper CMMC certification, you won’t be able to bid on certain contracts.
-
POA&M Limitations: While NIST 800-171 allows for POA&Ms, CMMC 2.0 is expected to have stricter limitations on the number and type of controls that can be on a POA&M at the time of certification, especially for CMMC Level 2.
In summary, the NIST 800-171 assessment process is the essential stepping stone to CMMC 2.0. By demonstrating robust implementation of NIST 800-171 and achieving a strong assessment score, you’re not just meeting current DoD requirements but also setting your organization up for success under the forthcoming CMMC framework.
How can you ensure ongoing NIST 800-171 DoD Assessment readiness?
Achieving a strong NIST 800-171 DoD Assessment score is a significant accomplishment, but compliance is an ongoing journey, not a one-time destination. Ensuring continuous readiness is paramount to maintaining contract eligibility and robust cybersecurity.
Here’s how to cultivate an ongoing state of NIST 800-171 DoD Assessment readiness:
-
Implement a Continuous Monitoring Program:
-
Don’t wait for the next assessment. Regularly monitor your systems and controls to ensure they remain effective.
-
This includes routine vulnerability scanning, log analysis, configuration audits, and intrusion detection.
-
-
Maintain and Update Documentation Religiously:
-
Your System Security Plan (SSP) and Plan of Action & Milestones (POA&M) are living documents. Update them whenever there are changes to your systems, personnel, or security posture.
-
Ensure all evidence of control implementation is readily available and current.
-
-
Regular Internal Reviews and Audits:
-
Conduct periodic internal reviews (e.g., quarterly or semi-annually) using the same DoD Assessment Methodology. This helps you catch issues before an official assessment does.
-
Treat these as mini-assessments to test your readiness.
-
-
Stay Informed of Updates:
-
Cybersecurity threats and DoD requirements evolve. Monitor updates from NIST (e.g., new revisions to SP 800-171) and the DoD (e.g., CMMC updates, new DFARS clauses).
-
Adjust your controls and processes as needed to align with the latest guidance.
-
-
Foster a Culture of Security:
-
Regularly train all employees on cybersecurity best practices, CUI handling, and your organization’s security policies. Human error remains a significant vulnerability.
-
Promote accountability for security across all departments.
-
-
Manage Third-Party Risk:
-
Extend your compliance efforts to your subcontractors. Ensure they are also meeting NIST 800-171 requirements and have current SPRS scores, as their non-compliance can impact you.
-
-
Leverage Automation and Tools:
-
Utilize governance, risk, and compliance (GRC) tools to help manage controls, track evidence, and monitor compliance status.
-
Automate security configurations and patching where possible.
-
-
Seek Expert Support When Needed:
-
Partner with cybersecurity and compliance experts, like GiaSpace, for periodic external validations, targeted remediation assistance, or to help navigate complex changes in regulations.
-
By embedding these practices into your operational rhythm, you transform NIST 800-171 compliance from a burdensome task into an integral part of your robust security strategy, ensuring perpetual assessment readiness.
Why should you consider expert help for your NIST 800-171 DoD Assessment?
Navigating the complexities of NIST 800-171 and the DoD Assessment requirements can be a daunting task, especially for organizations without dedicated in-house cybersecurity and compliance teams. While a self-assessment is mandated, seeking expert assistance can dramatically streamline the process, enhance your security posture, and significantly improve your assessment outcomes.
Here’s why partnering with a specialist like GiaSpace for your NIST 800-171 DoD Assessment is a strategic advantage:
-
Deep Expertise and Up-to-Date Knowledge: Cybersecurity regulations and threats are constantly evolving. Experts possess specialized knowledge of NIST 800-171, the DoD Assessment Methodology, DFARS clauses, and the latest CMMC 2.0 developments. They understand the nuances and can prevent costly misinterpretations.
-
Efficient Gap Analysis and Remediation: Experts can quickly identify compliance gaps using proven methodologies and help you develop actionable, efficient plans to address them. They know where common pitfalls lie and how to navigate them.
-
Objective Perspective: An external perspective offers an unbiased view of your cybersecurity posture, identifying blind spots that internal teams might overlook due to familiarity with existing systems.
-
Streamlined Documentation: Developing a comprehensive System Security Plan (SSP) and Plan of Action & Milestones (POA&M) is time-consuming. Experts can guide you through this process, ensuring your documentation is accurate, complete, and aligns with DoD expectations.
-
Preparation for All Assessment Levels: Whether you’re undertaking a Basic self-assessment or preparing for a potential Medium or High DoD assessment, experts can tailor their support to your specific needs, conducting pre-assessments and preparing you for auditor scrutiny.
-
Reduced Risk of Non-Compliance: By ensuring proper implementation and documentation, expert assistance significantly lowers your risk of non-compliance, avoiding potential contract loss, financial penalties, and reputational damage.
-
Focus on Core Business: Outsourcing the complex compliance burden allows your internal team to focus on your core manufacturing operations, increasing efficiency and productivity.
-
Access to Tools and Best Practices: Experts often utilize advanced tools and apply industry best practices that may not be available or known to every organization, enhancing the effectiveness of your security controls.
Investing in expert assistance for your NIST 800-171 DoD Assessment is an investment in your business’s security, compliance, and continued eligibility to serve the Department of Defense.
Getting Ready for CMMC
With the new CMMC framework, the DoD is working to level the cyber battlefield and keep ahead of cyberattacks that threaten the effectiveness of the U.S. military. CMMC is fast-tracked to be implemented in 2021 and fully implemented by 2025 across all contracts. We can help you prepare for CMMC compliance! GiaSpace offers comprehensive systems audits to identify gaps in your SSP and bring you one step closer to compliance. Contact us today for a consultation!
