Every April, millions of Americans Google “W-2 form” or “W-9 Tax Forms.” Normal stuff. Routine.
This year, some of those searches ended with attackers having full remote access to the victim’s computer and their security software completely disabled. And the victim had no idea any of it happened.
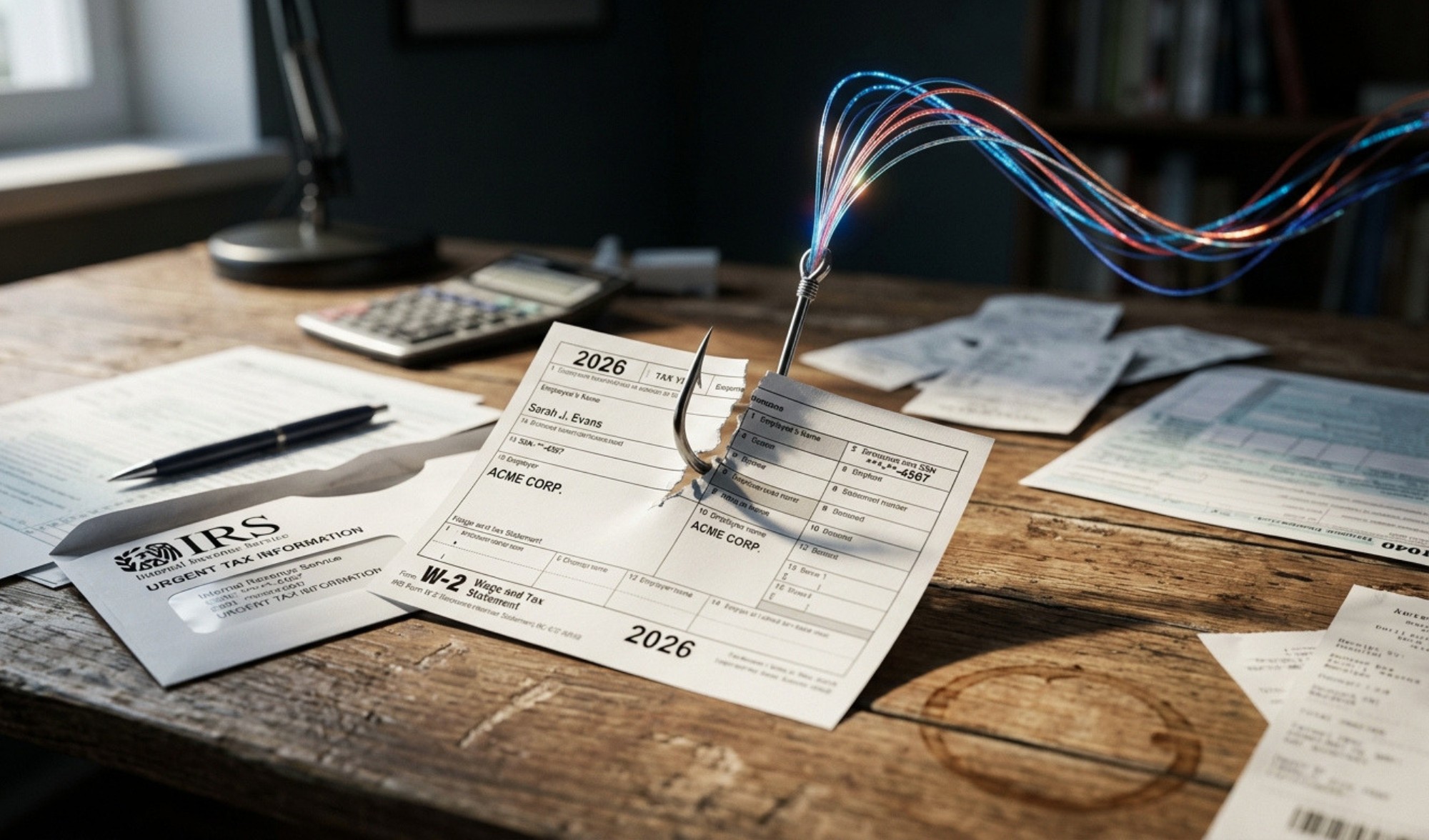
This is what tax season looks like in 2026.
The Google Ad That Wasn’t
Huntress researchers uncovered a malvertising campaign running since January 2026 that starts with something embarrassingly simple: a sponsored Google Ad for a tax form.
Someone clicks it, lands on what looks like an IRS compliance portal, and downloads what they think is a W-9 (because nobody has time to be suspicious in the middle of tax season). What they actually downloaded gave the attacker full remote access. From there, a tool called HwAudKiller silently killed Windows Defender, Kaspersky, and SentinelOne with no alerts and no warnings.
The cloaking software attackers used to fool Google’s ad reviewers? Bought commercially for $299 a month (because apparently that is a product that exists and is openly marketed with no content rules). Huntress confirmed over 60 malicious sessions tied to this campaign alone.
Why It Works Every Year
Microsoft Threat Intelligence tracked one campaign that hit 29,000 users across 10,000 organizations in a single day. Over 100 separate tax-themed campaigns have been recorded this year. The IRS put IRS impersonation at the top of its 2026 Dirty Dozen scam list. Again. For what feels like the hundredth year in a row.
Attackers love tax season because the conditions are perfect: deadlines make people click without thinking, the documents look familiar, and sensitive data is flying between accountants, employees, and platforms all at once.
What the Attacks Actually Look Like
This year’s campaigns are more varied than ever. Here is what your team needs to watch for:
- Fake Google Ads for tax forms. Sponsored results leading to fake IRS portals that deliver malware disguised as downloads.
- IRS impersonation emails. Subjects like “Irregular Tax Return Filed” or “2025 Employee Tax Docs” with attachments or QR codes leading to credential-stealing pages. Some include real IRS phone numbers to look official (the attention to detail is impressive, in the worst possible way).
- Fake HR requests for W-2s. Emails appearing to come from internal HR asking finance staff to confirm payroll or tax information. Accountants are the primary targets.
- AI-generated voice calls. Attackers using voice-cloning tools to impersonate your CPA or CEO asking to confirm banking details before a deadline. It sounds exactly like the person you think it is.
What To Do Before April 15
- Never download tax forms from a search result. Type IRS.gov directly into your browser. Bookmark it. Tell your team (it takes four seconds and would have stopped this entire campaign).
- Verify unexpected requests by phone. This can look like W-2 requests, wire transfers, and payroll confirmations. Call back on a number you already have, not one from the email.
- Check that your security software is actually running. HwAudKiller disables it silently with no alerts. Open your dashboard and confirm it is on before you find out the hard way.
- Enable MFA on everything tax-related. By everything, we mean payroll, accounting platforms, IRS online accounts, and banking portals (all of it!).
- Brief your finance and HR teams now. They are the most targeted roles this season and the least likely to think a W-2 email is suspicious.
The Bottom Line
2026 is the most active tax season for cyberattacks on record. The lures are convincing, the attack chains are sophisticated, and the window closes April 15.
The attackers know that. Make sure your team does too.
The businesses that don’t get breached aren’t lucky; they are prepared.
→ Schedule Your Free Security Assessment with Rob
→ Learn More About Our Managed Security Services
Published: Apr 2, 2026
Need IT Support for Your Florida Business?
GiaSpace provides proactive managed IT services, cybersecurity, and local tech support across Florida — with teams in Gainesville, Fort Lauderdale, Jacksonville, and Ocala.
Managed IT Services FloridaCybersecurity Services FLGainesville IT ServicesFort Lauderdale IT Services